SOC 2 Compliance in Austin, TX: What Most SaaS Startups Get Wrong in Year One
Austin’s SaaS ecosystem has grown substantially over the past decade, and with that growth has come a sharper expectation from enterprise buyers, investors, and procurement teams: show us your SOC 2 report. For many early-stage software companies, this request arrives before they have any formal security program in place. The response is usually a scramble — hiring a consultant, compressing a six-month process into eight weeks, and hoping the auditor doesn’t find anything too damaging.
What gets lost in that scramble is understanding. SOC 2 compliance is not a checkbox exercise. It is a structured evaluation of how a company actually manages security, availability, and confidentiality in its day-to-day operations. When founders and engineering leads treat it as a one-time hurdle rather than an ongoing commitment, problems surface quickly — often during renewal audits, customer due diligence reviews, or in the aftermath of an incident that could have been prevented.
This article is written for the people inside those companies making real decisions about how to approach compliance for the first time. The goal is to address the most common mistakes honestly, so teams can build a program that holds up under scrutiny rather than one that looks good on paper until it doesn’t.
Why the Austin SaaS Market Has Particular Pressure Around SOC 2
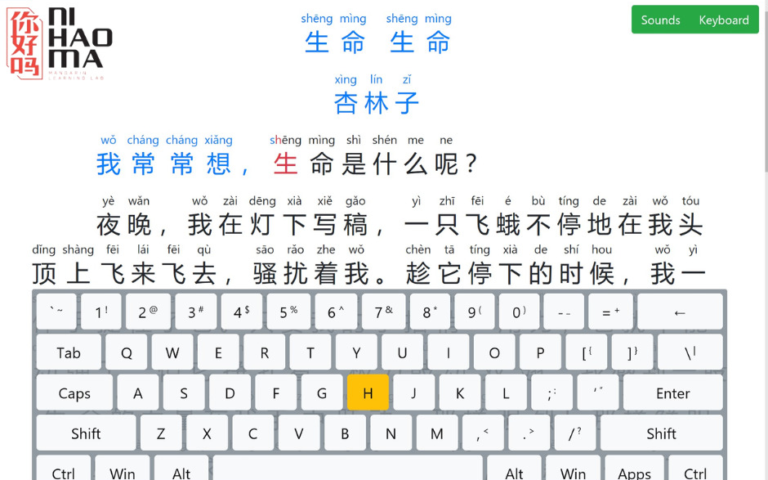
Austin has attracted a significant concentration of mid-market and enterprise software companies, along with the venture capital and private equity activity that accompanies that growth. That environment creates specific pressure around compliance because enterprise buyers in regulated industries — financial services, healthcare, logistics, government contracting — routinely require SOC 2 Type II reports before signing contracts. For a SaaS startup trying to move upmarket, the absence of that report is often a hard stop in procurement conversations. For teams just beginning to understand what that means, a practical Soc 2 Compliance Austin Tx guide can help establish what’s actually required before engaging an auditor.
The local market also has a talent dimension. As more security engineers and compliance professionals have relocated to or been trained in Austin, companies have more access to internal expertise than they did five years ago. That access, however, has not necessarily translated into better compliance programs. It has sometimes resulted in more sophisticated-sounding programs that still carry the same structural flaws as before.
The Gap Between Readiness and Appearance
One of the more consistent patterns in year-one compliance efforts is the distinction between appearing ready and being ready. A company can have a polished policy library, a completed security questionnaire, and a signed contract with an auditor — and still be fundamentally unprepared for the audit itself. This happens when the documentation doesn’t reflect actual operations, when controls exist on paper but haven’t been implemented consistently, or when the team responsible for evidence collection doesn’t understand what the auditor is actually looking for.
Preparation that focuses on documentation without verifying that underlying systems and processes match that documentation is one of the primary reasons first-year audits produce more findings than expected. The cost of those findings is not just remediation time — it’s delay, renegotiation with enterprise buyers, and sometimes the loss of a deal entirely.
The Type I vs. Type II Misunderstanding That Delays Deals
SOC 2 reports come in two forms. A Type I report reflects the design of controls at a single point in time. A Type II report reflects the operating effectiveness of those controls over a defined period, typically between six and twelve months. The distinction matters because most enterprise buyers, particularly in financial services and healthcare, require a Type II report. A Type I report demonstrates intent — it does not demonstrate that anything has actually been working reliably over time.
Many startups pursuing soc 2 compliance austin tx for the first time begin with a Type I report because it can be completed faster. That is a reasonable starting point, but it becomes a problem when the company presents that report to a prospect expecting a Type II, or when leadership assumes the Type I gets them across the finish line with enterprise buyers who are clear about their requirements.
Planning for the Audit Period Before the Audit Begins
The most practical implication of the Type I versus Type II distinction is that the observation period for a Type II audit has to actually happen before the audit can be completed. That means controls need to be operating, consistently, for months before the auditor arrives to collect evidence. If a company begins implementing controls the week before engaging an auditor, the earliest a credible Type II report can be issued is roughly nine to twelve months later.
This timeline is frequently underestimated. When a sales team promises a prospect that a SOC 2 Type II report will be delivered within three months, and the security program was started two weeks ago, the commitment cannot be honored without either misrepresenting the timeline or rushing a process that requires sustained, documented operation over time.
Selecting the Wrong Trust Services Criteria for the Business
The AICPA’s Trust Services Criteria form the foundation of every SOC 2 audit. The Security criteria, commonly called the Common Criteria, are required in every report. Beyond that, companies choose which additional criteria — Availability, Confidentiality, Processing Integrity, Privacy — apply to their product and their commitments to customers.
The mistake most early-stage companies make is either including too many criteria to appear comprehensive, or including criteria that don’t match what their customers actually care about. A startup offering a data analytics platform to healthcare organizations needs to think carefully about Confidentiality and potentially Privacy. A fintech company with uptime commitments in its service agreements needs to address Availability. Including criteria that don’t map to real customer obligations adds audit scope, increases cost, and creates evidence requirements the team isn’t equipped to meet.
Why Criteria Selection Affects Ongoing Operations, Not Just the Audit
When a company selects criteria during its first audit engagement, those criteria become part of its compliance program indefinitely. The controls designed to satisfy Availability criteria, for example, require ongoing monitoring, incident response documentation, and evidence of consistent performance over time. If the organization isn’t operationally prepared to sustain those requirements between audits, the next audit will produce findings regardless of how clean the first one was.
Criteria selection is not a strategic marketing decision about what looks good on a compliance page. It is a commitment to operational standards that have to be maintained in practice. Companies that approach it otherwise tend to discover the consequences during renewal.
Evidence Collection as an Afterthought
SOC 2 auditors do not take a company’s word that its controls are working. They collect evidence — logs, access reviews, configuration records, change management tickets, vendor assessments, training completion records — and evaluate whether that evidence demonstrates consistent control operation throughout the audit period. Evidence collection is where many first-year compliance programs fall apart, not because the controls weren’t running, but because no one was capturing proof that they were.
For companies pursuing soc 2 compliance austin tx, the practical problem is often organizational. Engineers are building product. Operations teams are managing infrastructure. Nobody has been formally assigned to capture and organize the evidence that an auditor will eventually need. When audit time arrives, teams are forced to reconstruct evidence retroactively, which is both time-consuming and, in some cases, simply not possible for events that were never logged.
Building Evidence Capture Into Daily Operations
The teams that handle audits most efficiently are the ones that treat evidence capture as a routine operational task rather than a pre-audit project. This means access reviews happen on schedule and are documented in a consistent format. Vulnerability scans run on a defined cadence and results are retained. Change management tickets reference the controls they relate to. Vendor security reviews are completed and stored in a location that the audit team can access without hunting through email threads.
None of this requires expensive tooling, though compliance automation platforms can help. It requires someone with clear ownership who understands what an auditor will ask for and ensures that documentation exists before it’s requested. That person is frequently missing in early-stage companies, and the absence is one of the most consistent drivers of audit delays and unexpected findings.
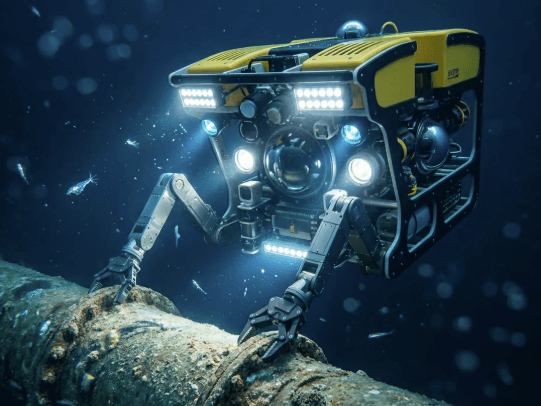
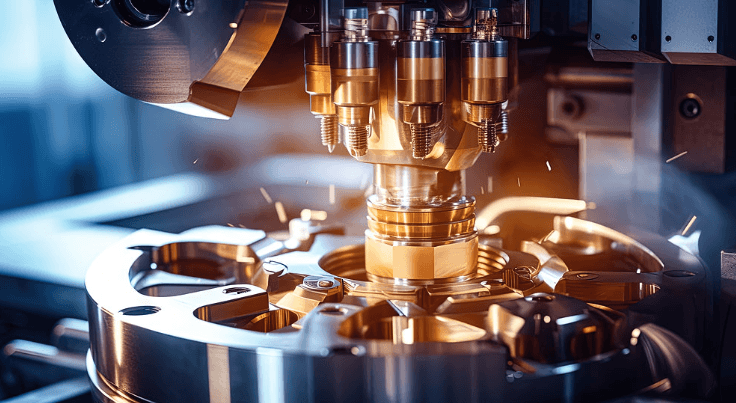
See also: Powering Industrial Progress with Advanced Motor Technology
Treating Compliance as a Security Program Rather Than a Business Commitment
SOC 2 is often framed internally as a security initiative. That framing is partially correct but frequently leads to misaligned expectations. The audit evaluates whether a company’s controls match the commitments it has made to customers — in service agreements, privacy notices, and sales conversations. If the sales team has told customers that data is encrypted at rest and in transit, that commitment will be tested. If the support team has access to production data without documented access controls, that gap will be flagged.
The compliance program cannot be owned exclusively by a security engineer or a CISO without input from legal, operations, product, and customer success. Each of those teams makes commitments that create compliance obligations. When those teams are not part of the soc 2 compliance austin tx conversation from the beginning, the audit scope doesn’t match reality, and the findings reflect that misalignment.
The Organizational Cost of Siloed Compliance
When compliance is treated as a security department project, other parts of the business continue making commitments and changing processes without understanding the implications. A product update that changes how customer data is stored, handled, or retained can affect multiple controls simultaneously. If product management doesn’t have visibility into the compliance program, and the compliance program doesn’t have visibility into the product roadmap, that change can create an undocumented gap that surfaces during the next audit.
Cross-functional awareness doesn’t require extensive training or formal governance structures in a small company. It requires that the person responsible for compliance has a regular line of communication with the people making decisions about data, access, and customer commitments. That communication loop is often the simplest and most undervalued element of an effective first-year program.
Closing Thoughts
First-year SOC 2 compliance for a SaaS startup is genuinely difficult, not because the standard is designed to be inaccessible, but because it requires operational consistency that early-stage companies are still building. The companies that complete their first audit cleanly are not necessarily the ones with the largest security budgets. They are the ones that started early enough, assigned clear ownership, and understood that the audit is evaluating real operations rather than documentation that describes ideal ones.
The mistakes covered in this article — confusing Type I with Type II, selecting criteria without operational planning, treating evidence as an afterthought, and siloing compliance within a single team — are correctable. They are also avoidable when leadership understands the actual shape of the commitment before signing with an auditor.
For companies in the Austin market facing soc 2 compliance austin tx requirements for the first time, the most useful thing is honest preparation: understand what the process requires, assess whether current operations can support it, and build the program around what’s actually true rather than what’s easiest to document. That approach takes longer at the outset, but it produces a compliance program that survives the second and third year without requiring the same scramble all over again.